Security
SOC 2 Compliance: Why It Matters for APIs
SOC 2 compliance for APIs: Core principles, trust categories, audit process, practical integration, and risks for software and enterprise teams.
NI
Nikolas Dimitroulakis
Last updated on December 22, 2025
SOC 2 Compliance: Why It Matters for APIs

Every American technology company faces growing scrutiny over customer data management, especially as more than 80 percent of businesses name cybersecurity as their top concern. Maintaining trust is not just about regulations, it is about proving robust controls and transparency at every step. Understanding SOC 2 compliance helps organizations navigate these demands by setting clear expectations and providing a pathway toward strong information security and operational reliability.
Table of Contents
- Defining SOC 2 Compliance and Core Principles
- SOC 2 Trust Service Categories Explained
- SOC 2 Audit Process and Key Criteria
- Integrating SOC 2 APIs Into Your Workflow
- Common Risks and SOC 2 Pitfalls to Avoid
Key Takeaways
| Point | Details |
|---|---|
| Understanding SOC 2 Compliance | SOC 2 is essential for technology companies to manage and protect customer data through rigorous evaluations of security and operational controls. |
| The Importance of Trust Services Criteria | Organizations must assess which Trust Services Criteria: Security, Availability, Processing Integrity, Confidentiality, and Privacy align with their operational needs for effective SOC 2 compliance. |
| Preparing for an Audit | Preparation is crucial; begin at least six months in advance to identify and address compliance gaps, ensuring a smoother audit process. |
| Continuous Improvement is Key | SOC 2 compliance is an ongoing commitment that requires regular risk assessments and updates to security controls to adapt to evolving threats. |
Defining SOC 2 Compliance and Core Principles
SOC 2 represents a critical framework for evaluating how technology companies manage and protect customer data. Developed by the American Institute of Certified Public Accountants (AICPA), this compliance standard focuses on ensuring that service organizations maintain robust security controls and data management practices.
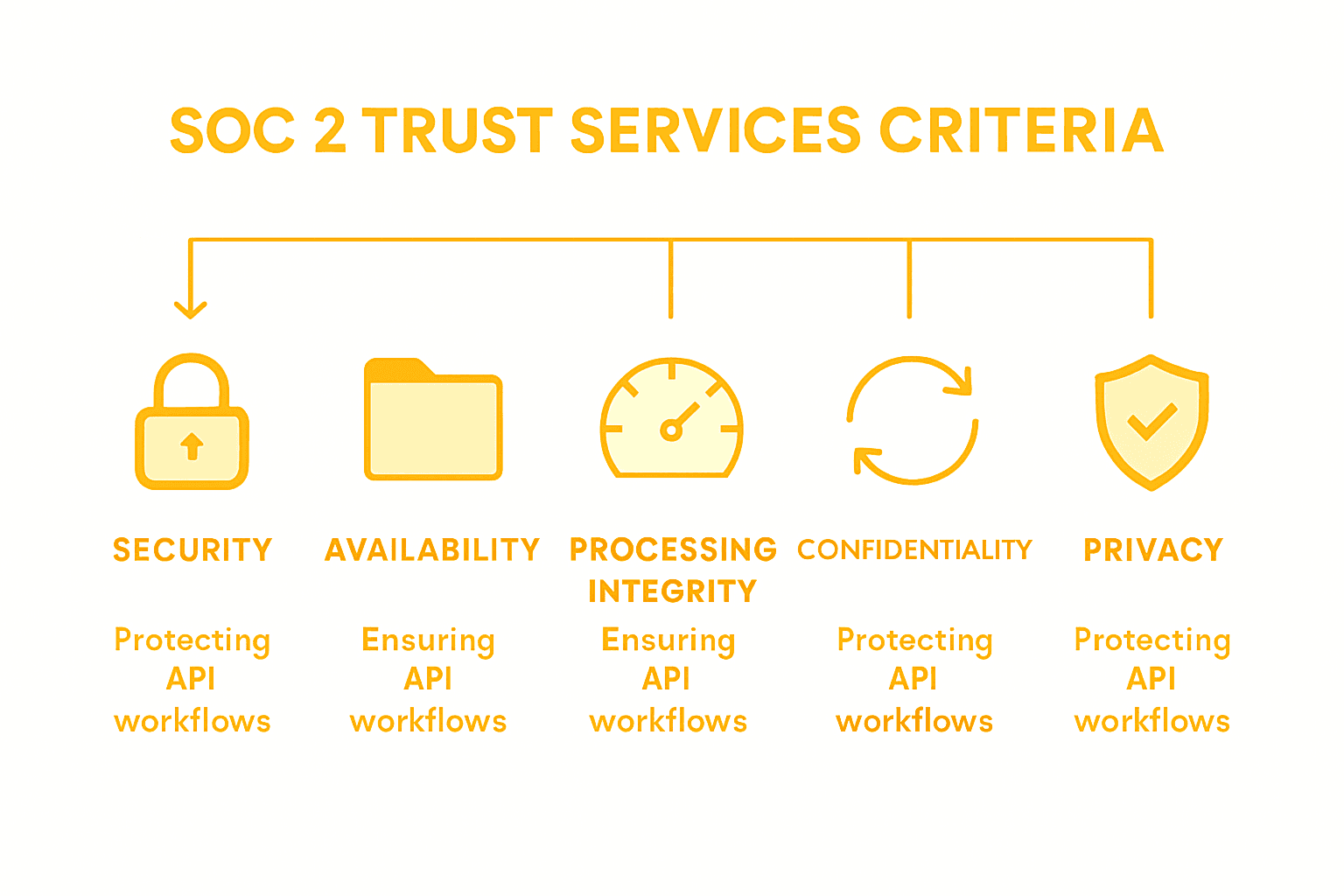
At its core, SOC 2 compliance involves an examination of controls across five key trust services categories: security, availability, processing integrity, confidentiality, and privacy. Each category addresses different aspects of data protection and operational reliability. The security category serves as the foundational criteria applied across all other categories, establishing baseline requirements for information security management.
The primary objectives of SOC 2 compliance include:
- Protecting sensitive customer information
- Establishing transparent data handling processes
- Demonstrating organizational commitment to security standards
- Creating verifiable audit trails for data management practices
- Reducing potential security risks and vulnerabilities
Organizations pursuing SOC 2 compliance undergo comprehensive assessments that evaluate their internal controls, technological infrastructure, and data governance strategies. These rigorous evaluations help build trust with customers, partners, and stakeholders by proving a systematic approach to data protection and operational excellence.
Pro Tip: Preparation Matters: Start preparing for your SOC 2 audit at least 6 months in advance by conducting internal readiness assessments and addressing potential compliance gaps before the official audit.
SOC 2 Trust Service Categories Explained
SOC 2 compliance encompasses five distinct Trust Services Criteria, each addressing a critical aspect of organizational data management and system reliability. These comprehensive categories provide a structured approach to evaluating an organization's security and operational practices.
The five SOC 2 Trust Services Criteria are mandatory and optional components that organizations can leverage based on their specific operational needs:
- Security: The foundational and mandatory category for all SOC 2 reports
- Focuses on protecting systems against unauthorized access
- Implements robust access controls and authentication mechanisms
- Ensures network and system infrastructure security
- Availability
- Evaluates system uptime and operational performance
- Assesses infrastructure reliability and disaster recovery capabilities
- Monitors system accessibility for authorized users
- Processing Integrity
- Confirms system processing completeness, accuracy, and timeliness
- Validates data processing workflows and transaction accuracy
- Ensures system outputs meet predefined quality standards
- Confidentiality
- Protects sensitive information from unauthorized disclosure
- Implements data classification and restricted access protocols
- Maintains strict information handling procedures
- Privacy
- Manages personally identifiable information collection and usage
- Ensures compliance with data protection regulations
- Establishes transparent data handling and consent mechanisms
While organizations can choose which categories beyond Security to include in their SOC 2 report, the specific selection depends on their service model, client requirements, and industry standards.
Here's a summary of the five SOC 2 Trust Services Criteria with typical organizations that benefit most from each:
| Trust Services Criteria | Main Focus | Benefiting Organizations |
|---|---|---|
| Security | Safeguarding data and systems | Cloud service providers |
| Availability | Ensuring uptime and resilience | SaaS and infrastructure vendors |
| Processing Integrity | Reliable, accurate processing | Payment processors |
| Confidentiality | Protecting private data access | Healthcare and legal services |
| Privacy | Managing personal data use | Marketing and consumer platforms |
Pro Tip: Strategic Selection: Carefully evaluate which Trust Services Criteria align most closely with your organization's operational model and customer expectations to create a comprehensive and meaningful SOC 2 compliance strategy.
SOC 2 Audit Process and Key Criteria
SOC 2 audits represent a comprehensive examination of an organization's control mechanisms, designed to validate the effectiveness of security, privacy, and data management practices. These rigorous assessments go beyond traditional compliance checks by providing a deep dive into an organization's operational controls and system reliability.
The audit process typically encompasses five critical evaluation areas:
- Control Environment
- Assesses organizational leadership and governance structures
- Evaluates commitment to maintaining robust security practices
- Reviews management's approach to risk management
- Risk Assessment
- Identifies potential technological and operational vulnerabilities
- Maps potential threats to existing control mechanisms
- Develops strategic mitigation strategies
- Information and Communication
- Evaluates internal communication channels
- Reviews data transmission and reporting protocols
- Ensures transparent information sharing mechanisms
- Monitoring Activities
- Tracks ongoing control effectiveness
- Implements continuous improvement processes
- Conducts regular internal and external assessments
- Control Activities
- Validates specific security and operational controls
- Confirms implementation of preventive and detective mechanisms
- Ensures alignment with industry best practices
The audit examines both the design and operating effectiveness of these controls, providing a comprehensive view of an organization's ability to protect sensitive information and maintain system integrity.
Organizations typically engage independent certified public accountants who specialize in SOC 2 assessments. These auditors use standardized frameworks to conduct thorough evaluations, generating detailed reports that demonstrate an organization's commitment to security and operational excellence.
Pro Tip: Documentation Mastery: Maintain comprehensive, real-time documentation of your control activities and regularly update your policies to demonstrate proactive governance during SOC 2 audits.
This table highlights the business impact of a successful SOC 2 audit:
| SOC 2 Audit Outcome | Business Benefit | Example Result |
|---|---|---|
| Clean audit report | Increased customer trust | More enterprise contracts |
| Identified weaknesses | Improved security posture | Remediation and policy updates |
| Ongoing compliance | Operational efficiency | Streamlined workflows |
Integrating SOC 2 APIs Into Your Workflow
Integrating SOC 2 APIs requires a strategic approach to aligning your technological infrastructure with rigorous security and compliance standards. This process involves implementing comprehensive controls that address critical trust service categories and ensure robust data protection across your API ecosystem.
Successful integration demands a multifaceted approach focusing on several key implementation strategies:
- Security Control Implementation
- Establish strong authentication mechanisms
- Implement granular access controls
- Create comprehensive logging and monitoring systems
- Develop robust encryption protocols for data transmission
- Access Management
- Design role based access control (RBAC) frameworks
- Implement multi factor authentication
- Create detailed user permission hierarchies
- Enable automated access review processes
- Data Protection Workflows
- Develop data classification schemas
- Create clear data handling and retention policies
- Implement secure data transmission protocols
- Establish transparent data privacy mechanisms
- Continuous Monitoring
- Set up real time security event tracking
- Develop automated compliance verification systems
- Create incident response and remediation workflows
- Implement regular security assessment procedures
By systematically addressing the five Trust Services Criteria, organizations can transform SOC 2 compliance from a complex challenge into a strategic advantage. This approach not only mitigates security risks but also demonstrates a commitment to maintaining the highest standards of data protection and operational integrity.
APIDevOps teams should view SOC 2 integration as an ongoing process of continuous improvement, regularly reassessing and updating their control mechanisms to adapt to evolving technological landscapes and emerging security threats.
Pro Tip: Compliance Automation: Invest in automated compliance monitoring tools that can continuously track and validate your SOC 2 control implementations, reducing manual overhead and providing real time insights into your security posture.
Common Risks and SOC 2 Pitfalls to Avoid
Organizations frequently encounter critical challenges when pursuing SOC 2 compliance, often underestimating the complexity of maintaining robust security and operational controls across their technological infrastructure.
Key risks and potential compliance pitfalls include:
- Inadequate Security Controls
- Incomplete access management protocols
- Weak authentication mechanisms
- Insufficient user permission granularity
- Lack of comprehensive monitoring systems
- Documentation Gaps
- Inconsistent policy documentation
- Outdated security procedure records
- Missing incident response protocols
- Incomplete control implementation evidence
- Compliance Misconceptions
- Treating SOC 2 as a one-time certification
- Overlooking continuous improvement requirements
- Failing to integrate compliance into daily operations
- Underestimating the scope of trust services criteria
- Technical Implementation Errors
- Poor encryption strategy
- Ineffective data classification systems
- Inadequate network segmentation
- Inconsistent logging and audit trail maintenance
- Vendor and Third-Party Risks
- Insufficient vendor security assessments
- Lack of comprehensive third-party risk management
- Overlooking subcontractor compliance requirements
- Inadequate contractual security provisions
Successful SOC 2 compliance demands a holistic approach that transcends mere technical configurations. Organizations must cultivate a comprehensive security culture that embeds compliance principles into every operational layer, transforming regulatory requirements from bureaucratic checkboxes into genuine security enhancements.
Technology teams should view SOC 2 compliance as an ongoing journey of continuous improvement, requiring persistent vigilance, regular assessments, and proactive risk management strategies.
Pro Tip: Risk Assessment Mastery: Conduct quarterly comprehensive risk assessments that systematically evaluate your existing controls, identifying potential vulnerabilities and implementing preemptive mitigation strategies before they become significant compliance challenges.
Simplify SOC 2 Compliance with Trusted API Integrations
Achieving and maintaining SOC 2 compliance demands rigorous security controls and seamless data management strategies. If you are looking to reduce risks such as inadequate access management or documentation gaps while accelerating your product development, leveraging ready-to-use, secure APIs is a game changer. ApyHub’s extensive API marketplace offers reliable solutions that align with key SOC 2 principles like security, confidentiality, and monitoring activities. Using trusted APIs cuts down implementation errors and streamlines continuous compliance efforts.
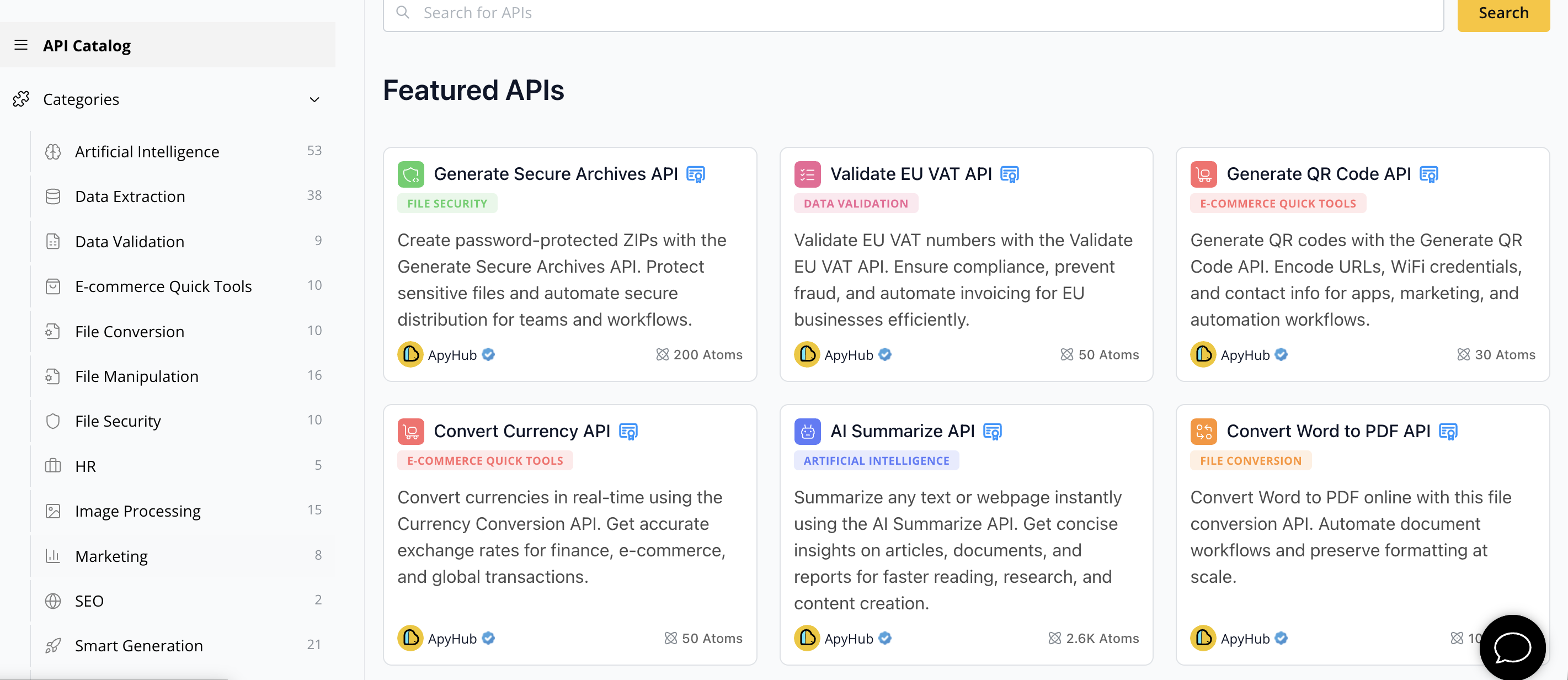
Explore our curated APIs designed to support practical SOC 2 integration patterns and real-world workflows. Whether you need help with secure data extraction, file security, or authentication controls, we have ready-made APIs to enhance your technological infrastructure. Start now by visiting the ApyHub catalog to confidently advance your SOC 2 journey and build trust through robust, compliant API integrations.
Frequently Asked Questions
What is SOC 2 compliance?
SOC 2 compliance is a framework designed to evaluate how service organizations manage and protect customer data, focusing on security, availability, processing integrity, confidentiality, and privacy.
Why is SOC 2 compliance important for API security?
SOC 2 compliance is crucial for API security as it ensures that organizations implement robust security controls and data management practices, thereby protecting sensitive customer information and maintaining operational integrity.
How does the SOC 2 audit process work?
The SOC 2 audit process involves a comprehensive examination of an organization's control mechanisms, evaluating areas such as control environment, risk assessment, information and communication, monitoring activities, and control activities to validate their effectiveness in protecting data.
What common risks should organizations avoid when pursuing SOC 2 compliance?
Organizations should avoid risks such as inadequate security controls, documentation gaps, compliance misconceptions, technical implementation errors, and vendor or third-party risks to ensure a successful SOC 2 compliance journey.

